Duration: 2 hours
Audience: Hardware engineers, Embedded developers, product security teams, IoT manufacturers
Level: Advanced
Price: This session is available in live sessions or as a package to deploy on your internal training platform

Hardware and firmware are common targets for attackers. They can exploit products by reversing firmware, discover secrets and modify the intellectual property. They can also exploit insecure firmware update processes to launch large-scale attacks against all products.
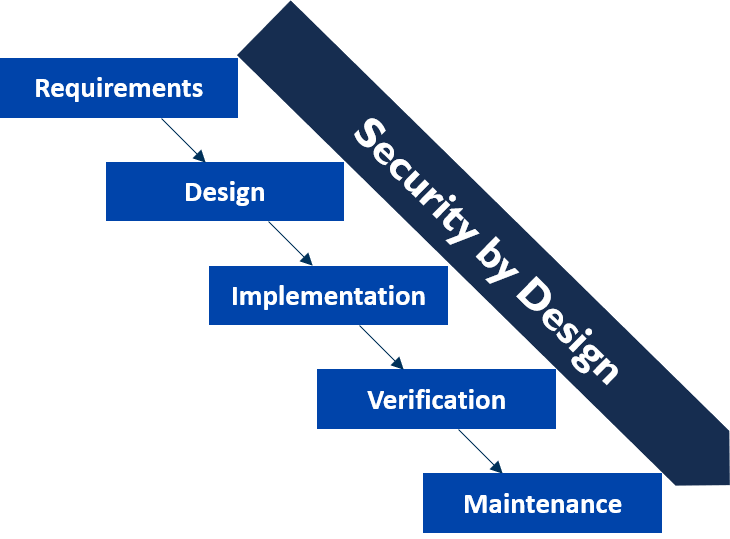
This 2-hour awareness session explains the potential threats and mitigation to better protect IoT devices against physical, network and software-based attacks. You will discover the risks of insecure hardware and firmware, and learn about important concepts to secure devices against hardware-based attacks, software-based attacks (example: reversing), and network-based attacks (interception/injection). We will also look at securing the development environment against supply-chain attacks.
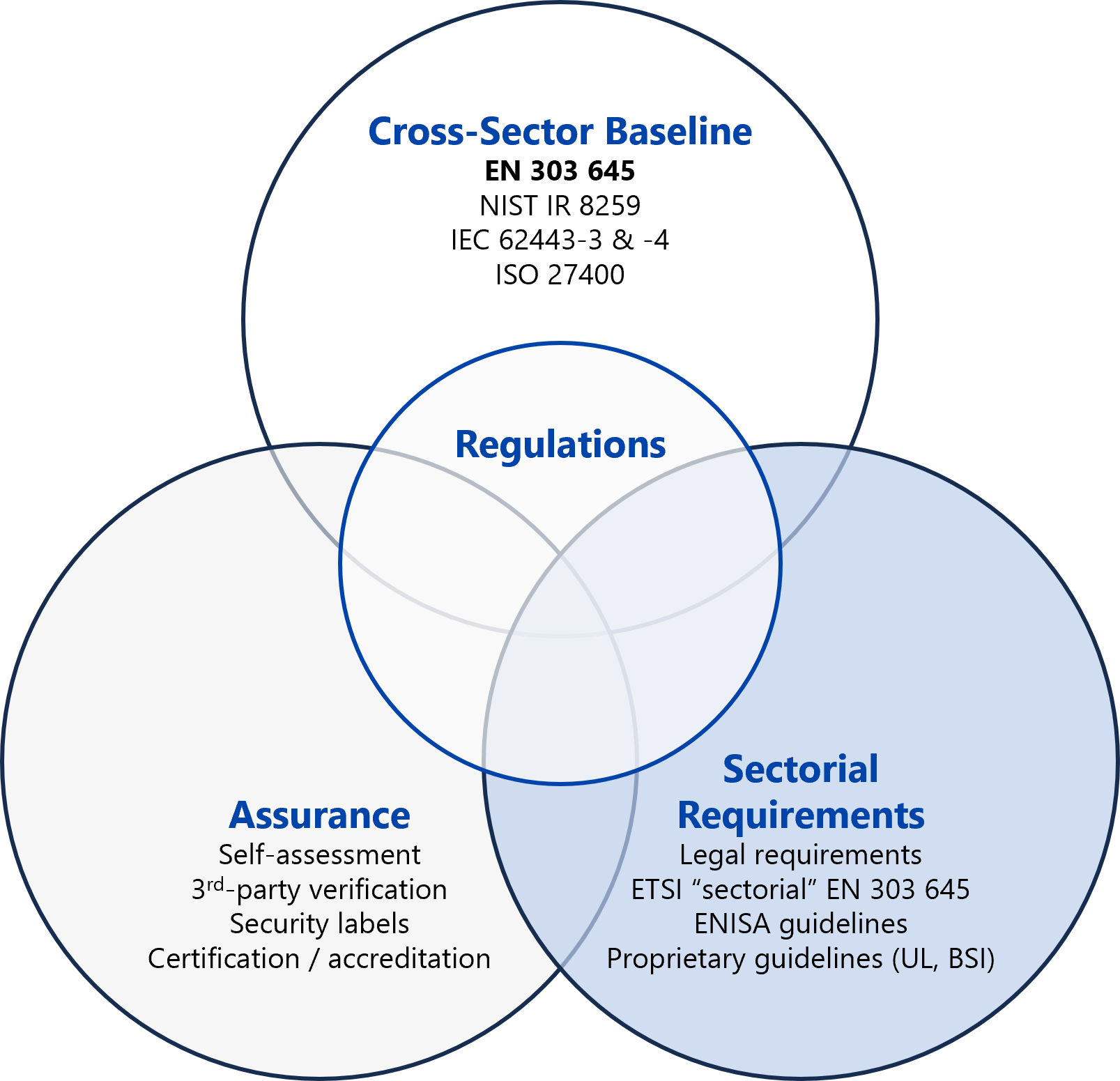
This session will help you better comply with provision 5.4 of ETSI EN 303 645. This training course is ideal for anyone involved in implementing products firmware.
This session is available in live session or as a package that you can deploy on your internal training platform. The content remains accessible to non-security experts. There is no coding and no hacking involved.
Objectives:
- Know the threats to and risks of insecure firmware and hardware
- Be able to identify appropriate security requirements to secure firmware development and devices against physical attacks
- Know how to protect firmware end-to-end
Programme:
- Presentation of attacks against hardware and firmware
- Cyber security requirements to protect devices against hardware, software and network attacks
- Cyber security requirements to protect firmware development and supply-chain security