Conceiving secure products at scale is a complex challenge. With the Internet of Things (IoT), products become cyber-physical systems that bring new functionalities, optimised operations and emerging business models. Yet, they also create new risks on data protection and safety.
cetome accompanies you
With cetome, manufacturers improve their visibility across multi-brand, multi-market portfolios. Your secure product strategy becomes:
An accelerator to product release
Unified across your portfolio
Immune to uncertainty
Financially efficient
Our services for product security
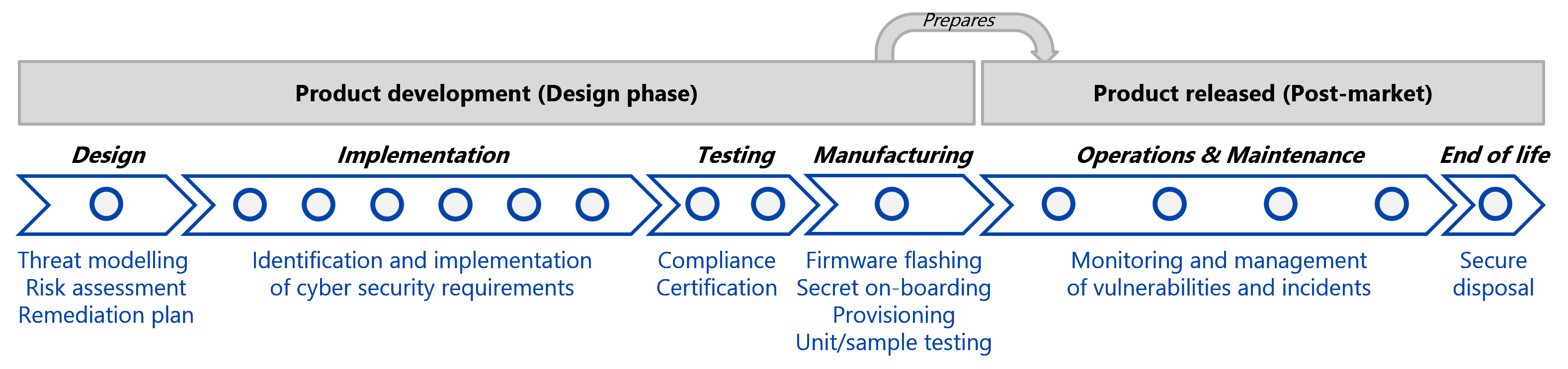
We support the entire product lifecycle, from inception to end-of-life.
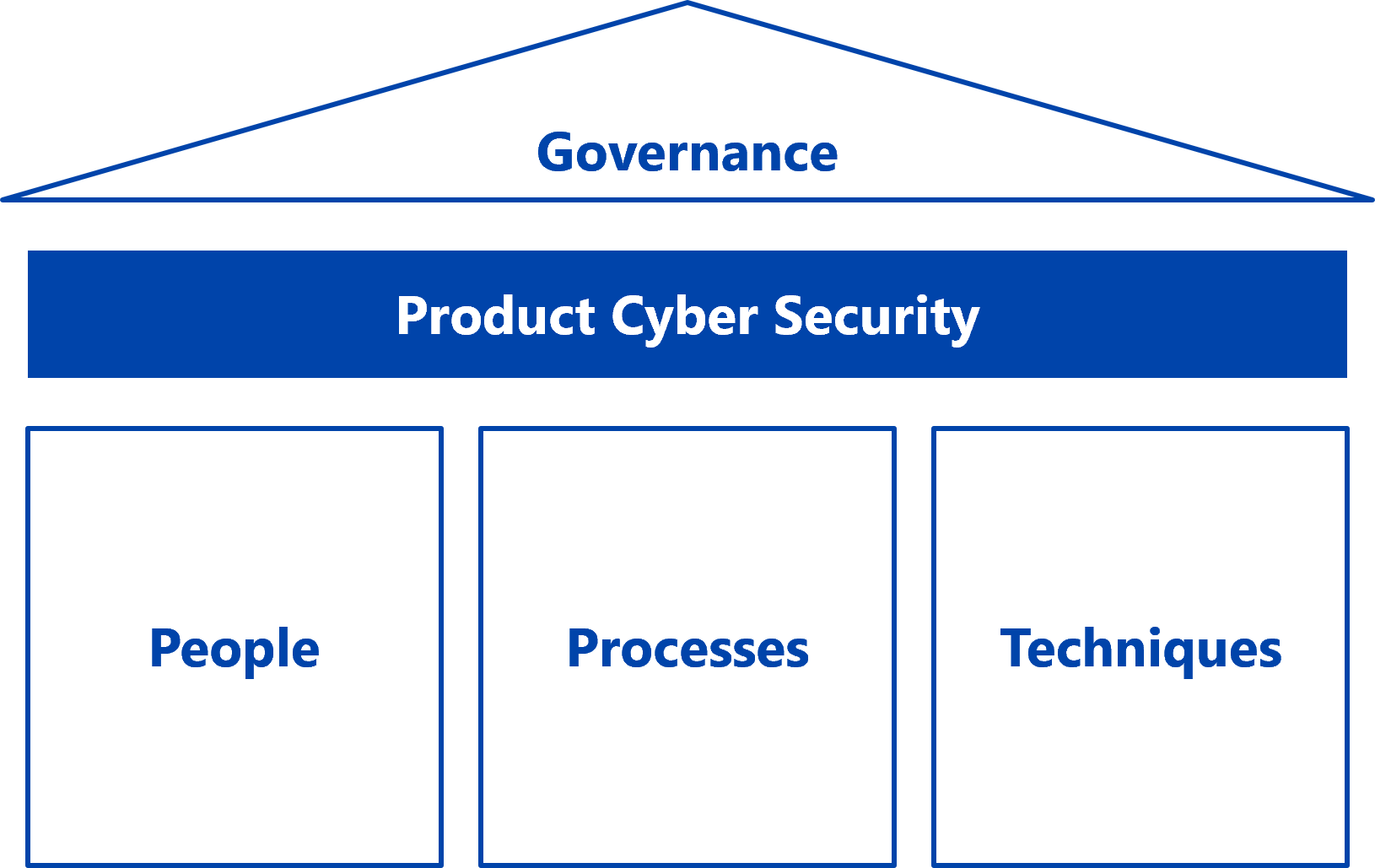
Product security governance
Govern your global portfolio with precision with executive dashboards and actionable KPIs that translate complex topics into strategic clarity.
By consolidating your governance, you secure a budget with total transparency while defining a robust internal organisation.
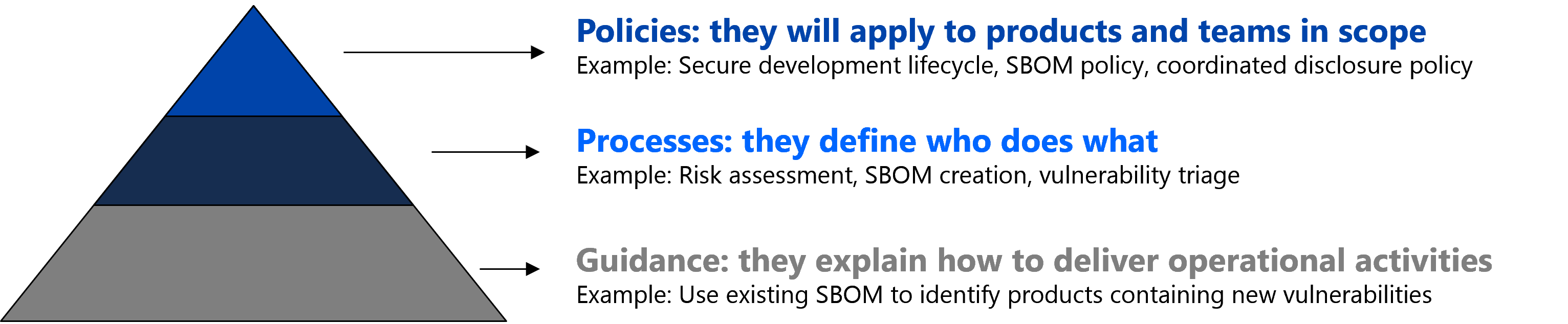
Policies and Processes
Benefit from clear decision-making by empowering your teams with clear responsibilities and enforceable milestones.
We review or architect your policies and processes, to ensure they work for you, providing the foundations to a secure product portfolio.
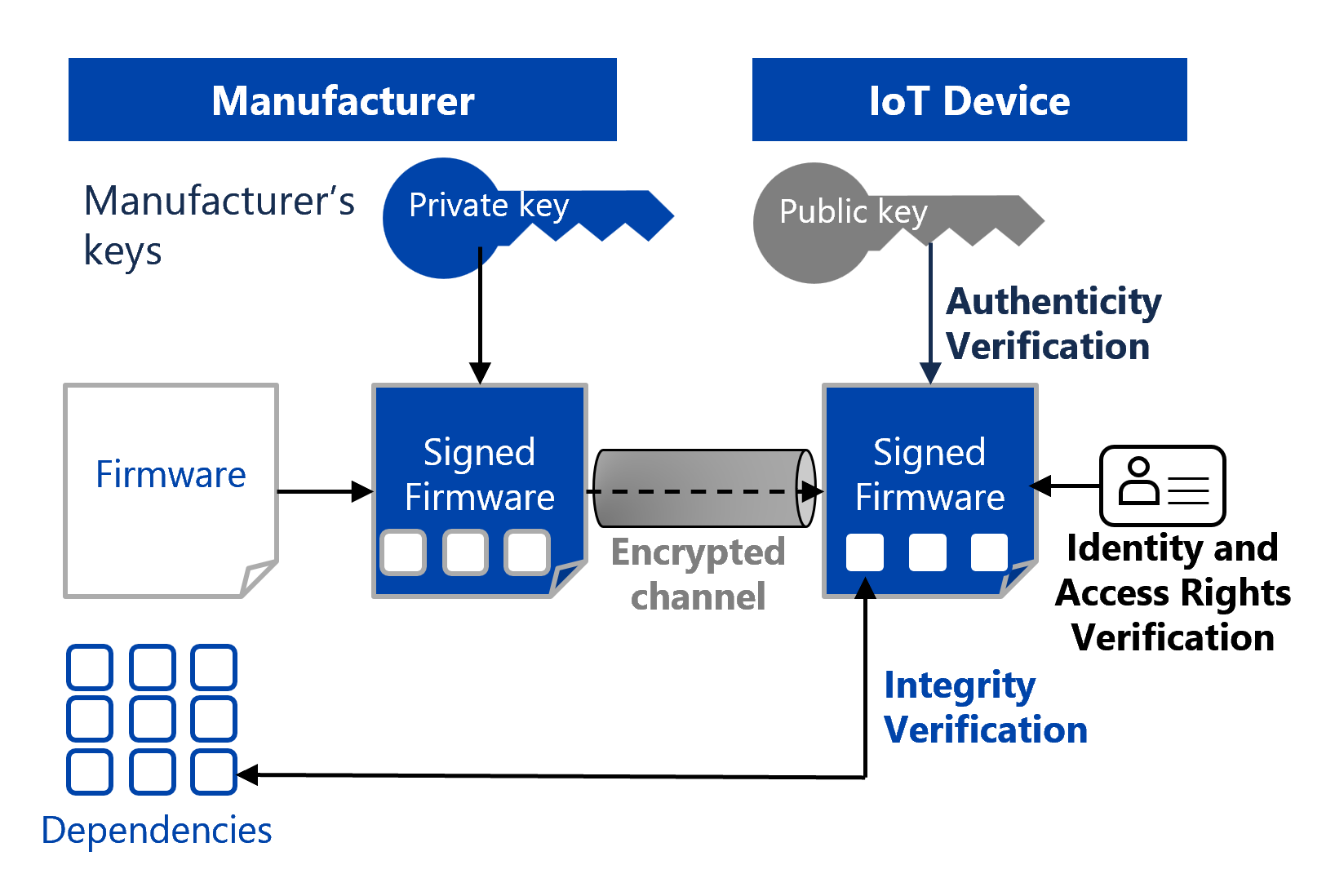
Security-by-design
Accelerate the product lifecycle to protect your innovation without compromising your speed-to-market.
By securing products from their inception, you eliminate the need for late-stage redesign, reduce cyber risks and simplify compliance.
Resilient Architecture
Adopt a resilient security architecture across your entire portfolio to optimise development costs while minimising your global attack surface.
By following a unified approach, you avoid technical debt and ensure consistency across every product and market.
Supply chain management
Orchestrate the strategic alignment of your third-party ecosystem ensuring your partners meet your requirements.
By better controlling your entire value chain, upstream and downstream, you reduce product vulnerabilities and risks to your users.
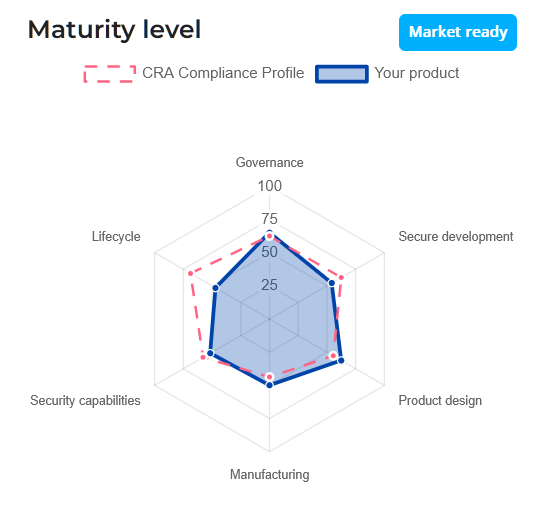
Maturity level evaluation
Align your governance and operations to maximise your investments and achieve a future-proof posture.
Benchmark your market-readiness across global regulations to pinpoint critical gaps and accelerate your path to full compliance.