Since August 2025, wireless products must implement cyber security requirements to receive the CE mark. The Radio Equipment Directive Delegated Act (RED cyber) is an important shift: manufacturers must integrate mandatory cyber security requirements into their connected devices, and document them accurately.
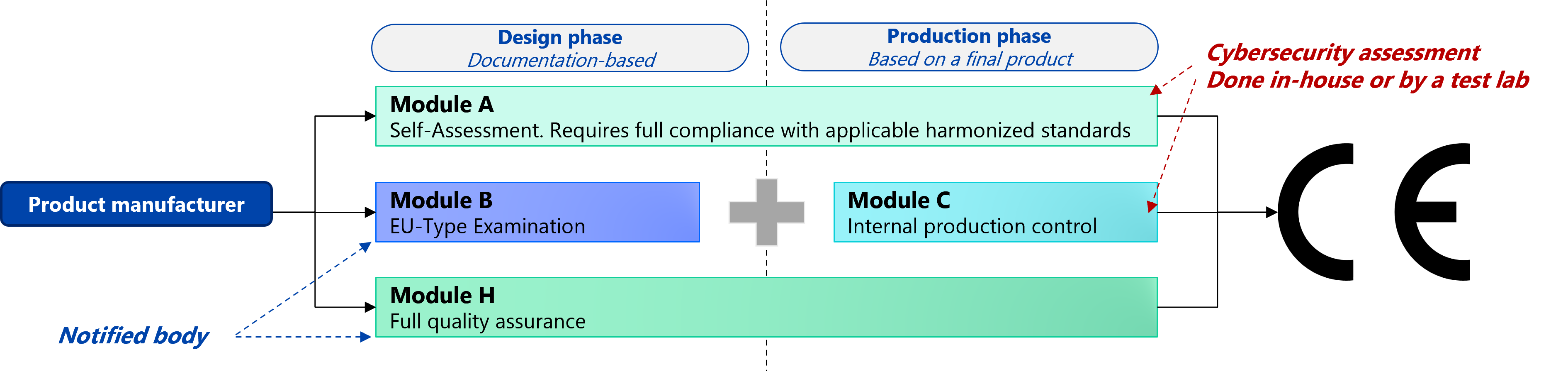
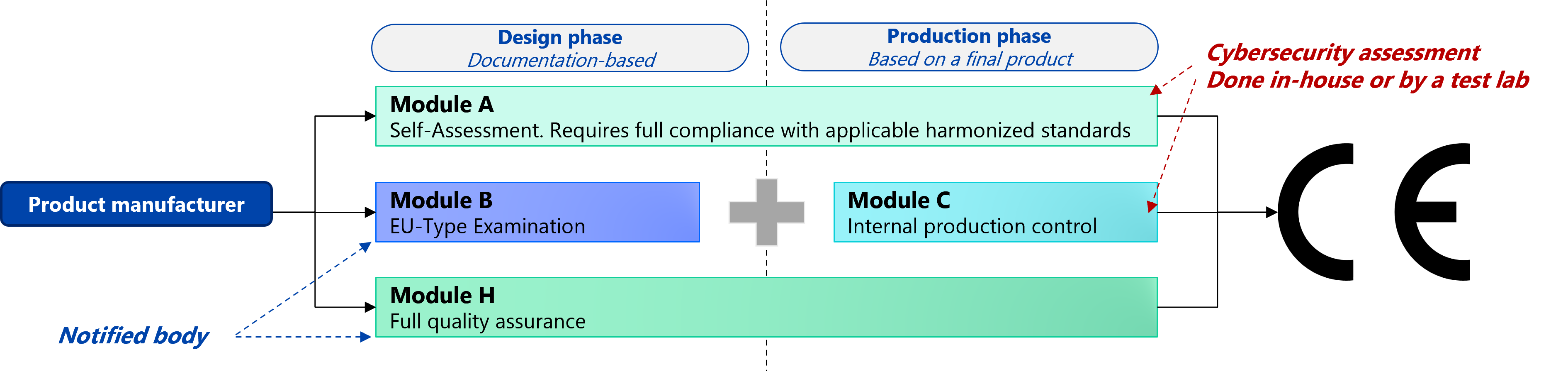
Manufacturers must then verify their product compliance using either:
- Self-assessment, which is only possible when adopting the harmonised standard hEN 18031 (with restrictions).
- EU-Type examination by a Notified Body, which guarantees the highest level of assurance.
A Notified Body is mandatory when using another standard such as EN 303 645 or IEC 62443-4-2.
cetome accompanies you
We work with product manufacturers to make their products:
Stronger against risks
Faster on the market
Better prepared to CE requirements
Ready for CRA compliance
Services for RED compliance
We designed our services to support you at every stage of your RED compliance journey.
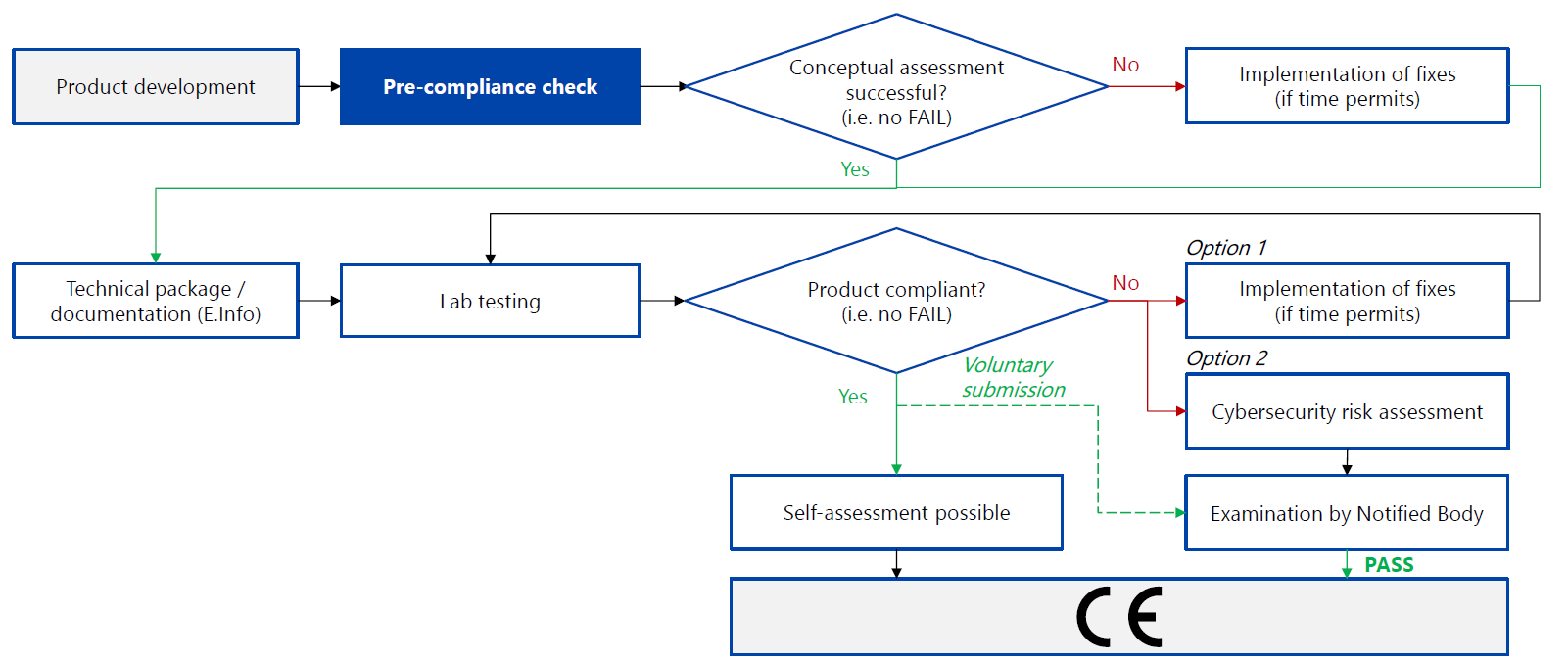
Pre-compliance check
Evaluate the market-readiness of your product with RED harmonised standards to close structural gaps before it impacts your release timeline.
Benefit from this proactive approach to improve your product at an accessible price.
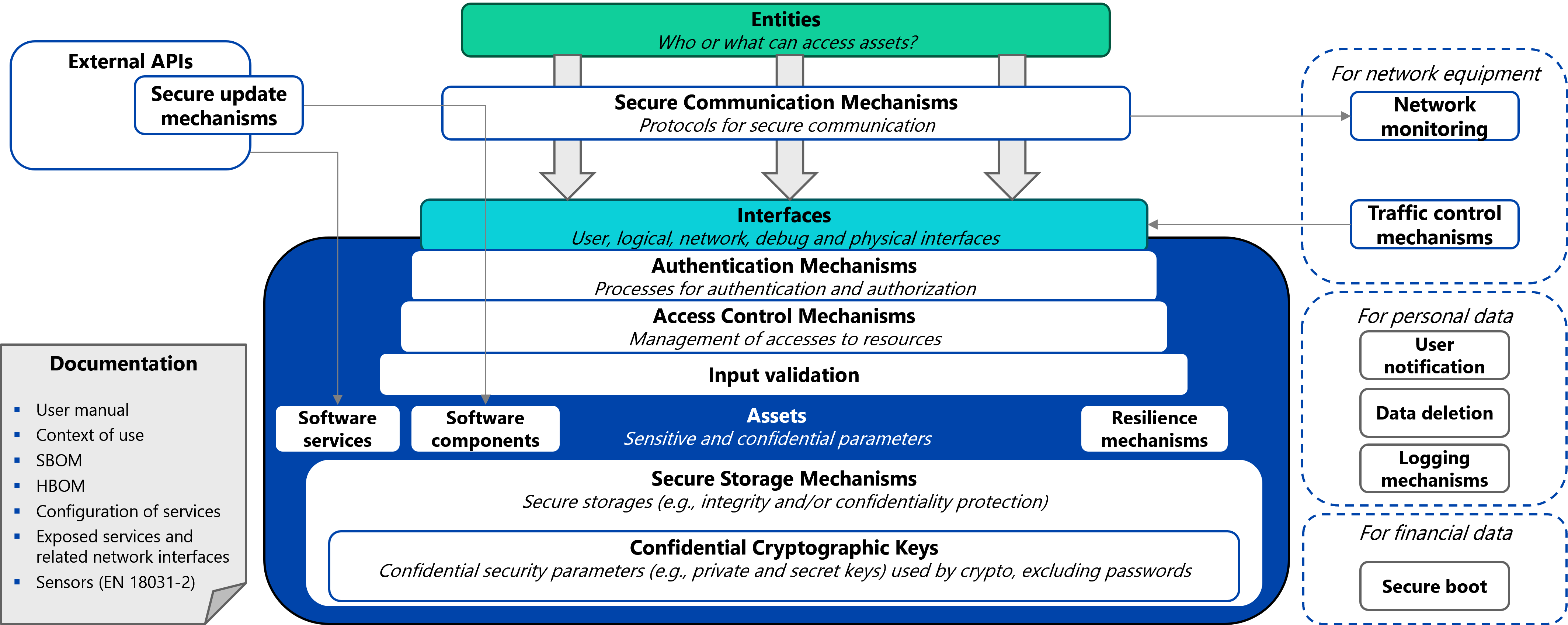
Architecture engineering
Integrate a unified architecture that bridges the gap between product constraints and RED requirements to eliminate costly last-minute redesign.
From hardware root-of-trust to mutual authentication, secure your products against cyber attacks.
Compliance roadmap
Optimise governance by defining key actions, milestones, and required resources to align technical execution with business objectives.
This service helps you focus on priorities and secure a budget in preparation of the Cyber Resilience Act.
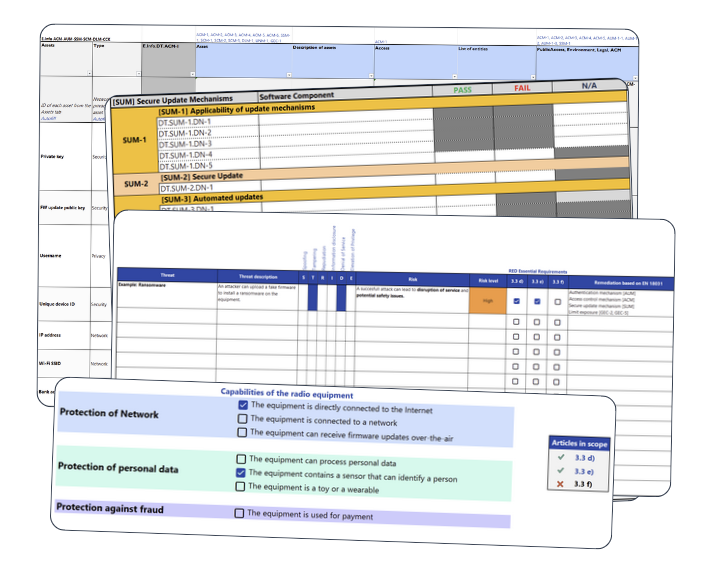
Cyber security risk assessment
Formalise your secure-by-design approach and justify your architectural choices.
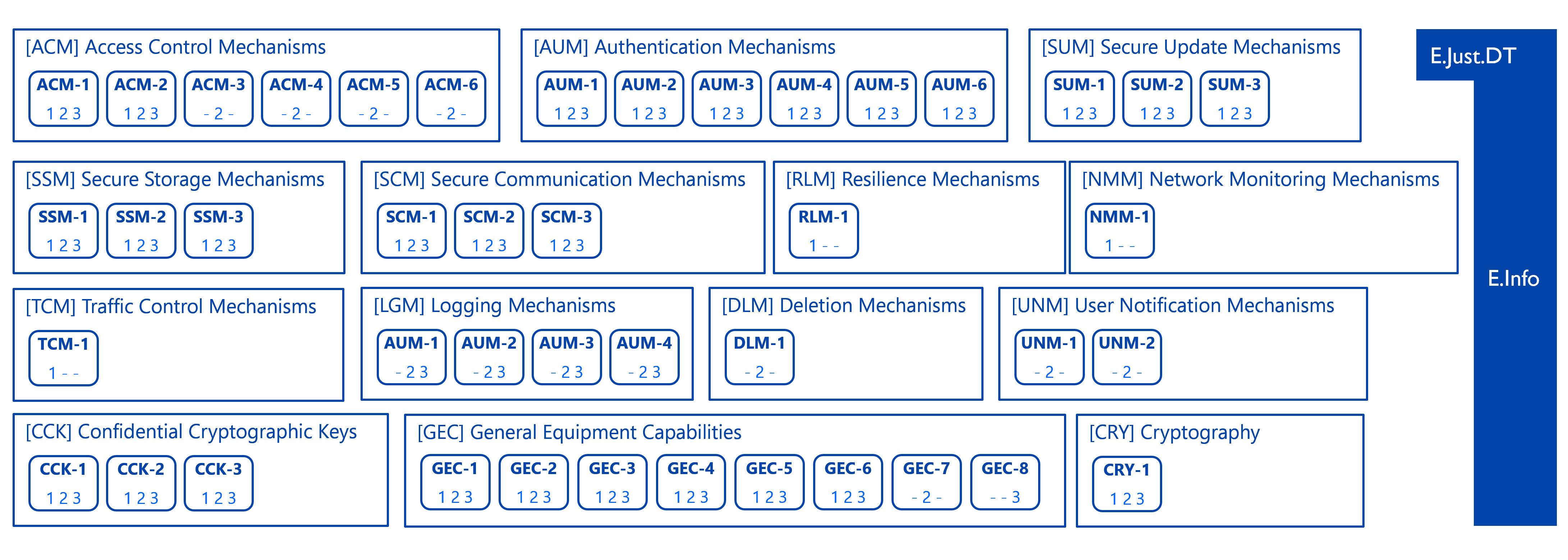
This is an important step to protect of your assets with appropriate security mechanisms.
Technical documentation
Ensure your technical E.Info documentation is accurate and ready for certification.
To prepare your documentation, get our free REDact toolkit!
Liaison with test lab
Accelerate time-to-market by leveraging our expertise to interpret lab results and resolve non-conformities.
We accompany you until you pass!
Note: we have 100% success-rate!