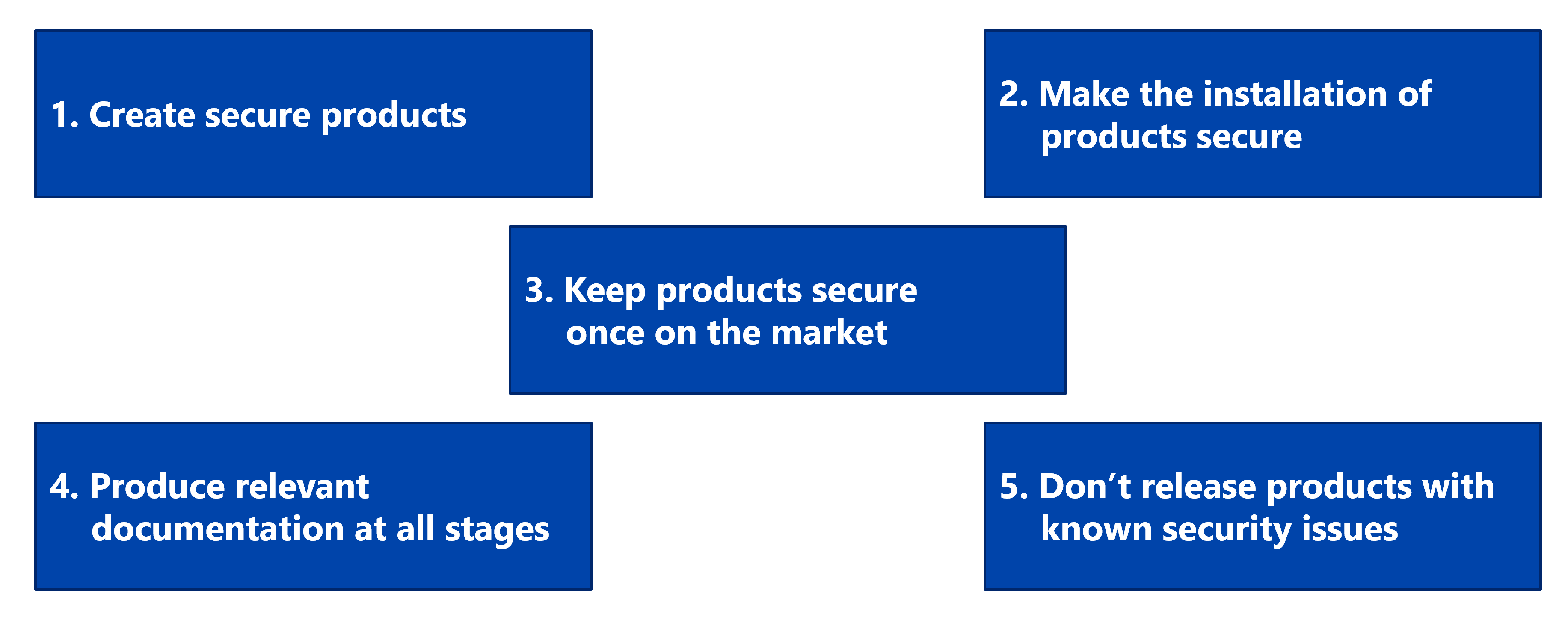
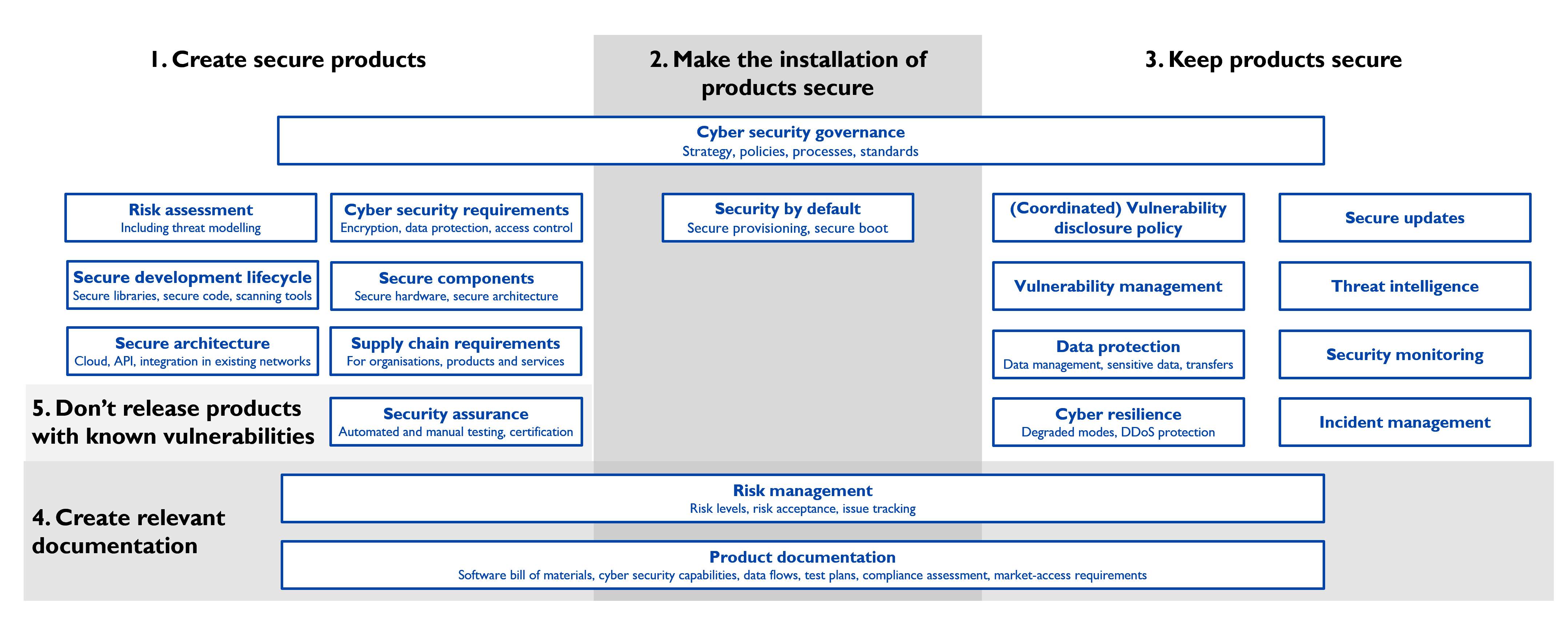
The Cyber Resilience Act (CRA) mandates cyber security requirements in products. This mix of governance and technical requirements covers the entire lifecycle of products in scope, and beyond (10 years!).
The CRA becomes applicable from 11th of September 2026, with full compliance required starting the 11th of December 2027.
cetome accompanies you
With cetome, easily navigate these obligations from initial design to long-term vulnerability reporting. Your products become:
Resilient to risks
Secure by design
Vulnerability-proof
Market-accelerated
Our services for CRA compliance
We designed our services to support you at every stage of your CRA compliance. We cover all product categories.
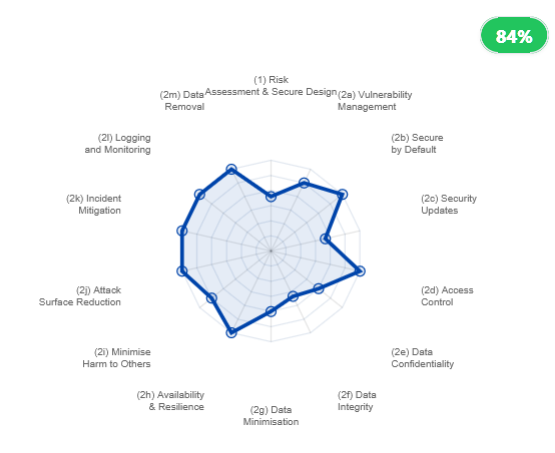
Risk assessment
Formalise your secure-by-design approach by integrating a risk-based approach.
The risk assessment is the most important requirement to achieve CRA compliance.
Gap Analysis
Evaluate the market-readiness of your products with CRA Essential Requirements to close structural gaps before it impacts your release timeline.
Benefit from this proactive approach to evaluate your products at an accessible price.
Compliance roadmap
Optimise governance by defining key actions, milestones, and required resources to align technical execution with business objectives.
This actionable roadmap will consolidate your budget forecast.
Security-by-design
Integrate secure-by-design principles in your development process to better protect products throughout their lifecycle.
By leveraging this CRA requirement, you simplify your implementation of product cyber security.
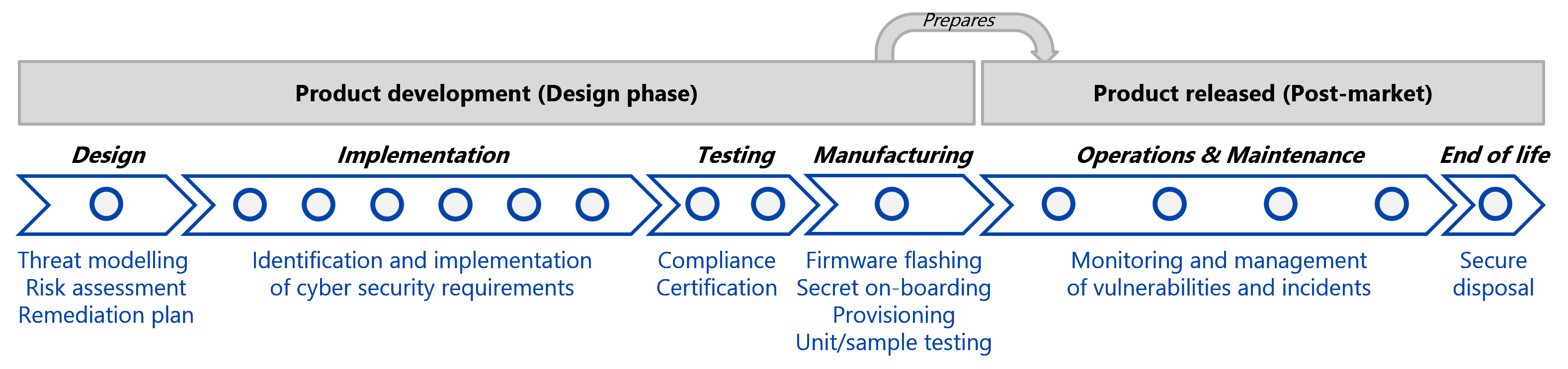
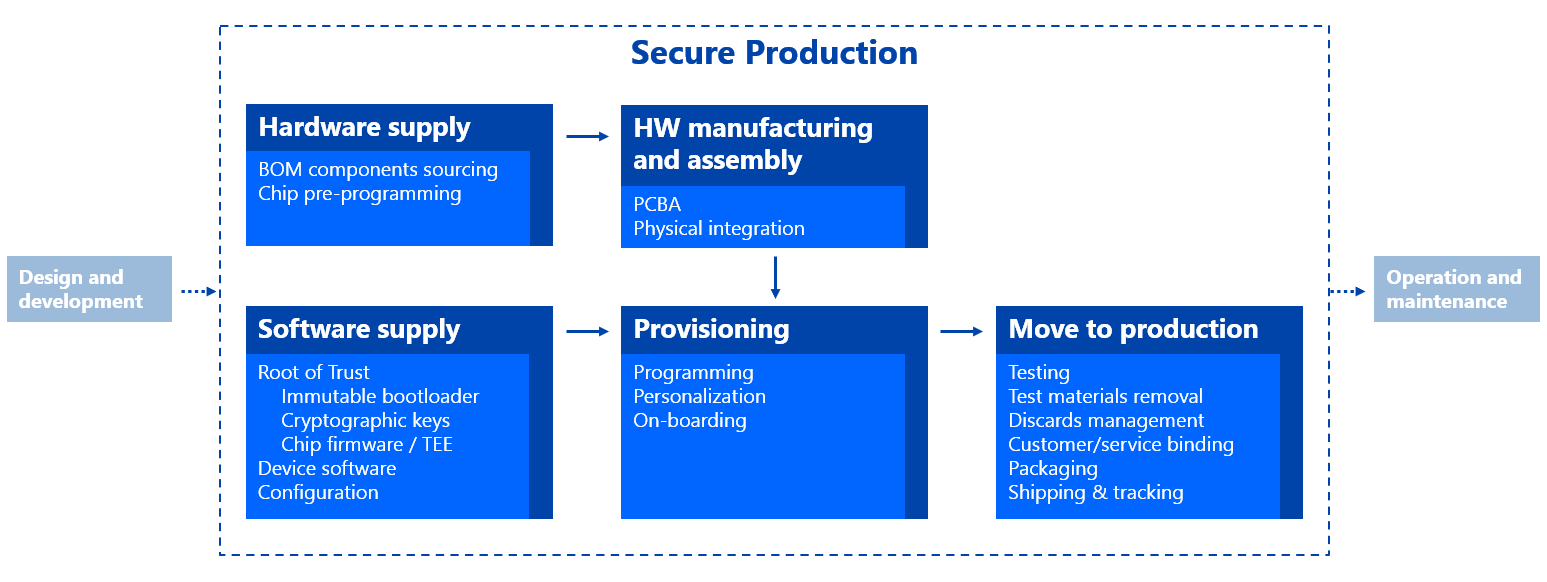
Threat model for manufacturing
Identify threats and risks related to the production phase, covering both internal and external factories, to meet your mandatory CRA requirements.
Don’t miss out! You must demonstrate that your products are produced securely.
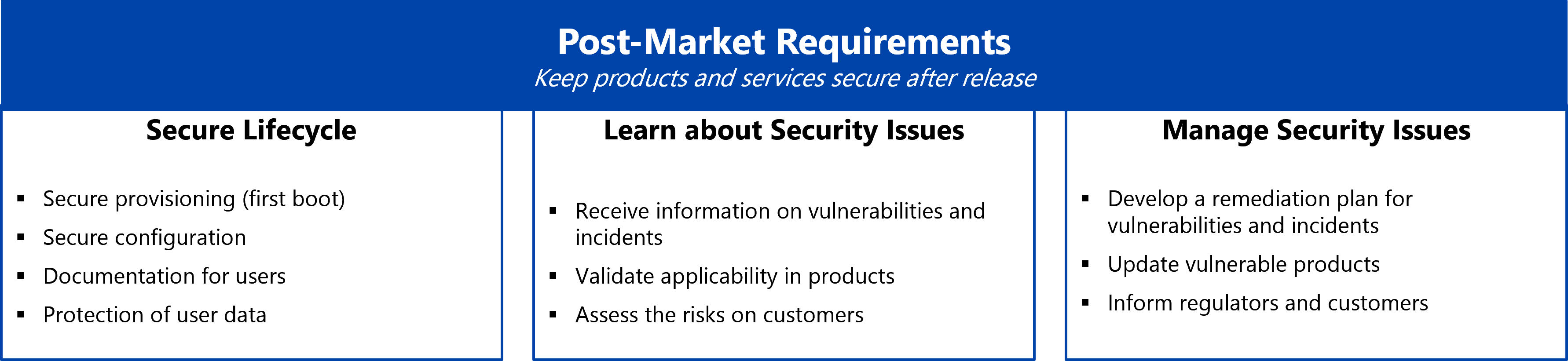
Post-market requirements
Establish policies and processes to comply with your reporting obligations and leverage SBOM for automating vulnerability management.
Keeping products secure after release by managing cyber security issues will help you avoid crises and consolidate customer trust.